CSEC 331 Stetson University Pentesters 2019


“A penetration test, colloquially known as a pen test, pentest or ethical hacking, is an authorized simulated cyberattack on a computer system, performed to evaluate the security of the system.”
-Wikipedia
For eleven years Dan Plante, professor of math and computer science, has had his upper-level computer science class conduct “live” penetration testing or ethical hacking of Stetson University’s computer network and systems. While it might seem as if other colleges and universities would be doing the same thing, Plante says a lot of programs limit penetration testing and hacking to mock servers specially set up for the classroom environment.
“This is a truly unique opportunity,” said Plante. “I’ve been to a number of conferences and have talked with my colleagues and have yet to find another university doing this.”

When he started, “It was a lot easier,” said Plante. Now? “Much harder.”
You might think Stetson’s IT department would find this annual effort troubling, problematic or even irritating, but not so, says Jose Bernier, Stetson’s CIO and associate vice president for Information Technology.
“We bring in security agencies to do annual audits,” said Bernier. “But the computer science students have very creative approaches, and they have the time to look for the less visible access points. Each year when we get their report it helps improve the university’s security.”
With 3,000 plus computers and multiple access points, Bernier says it helps to have a second set of eyes on the system’s vulnerabilities. Plante and Josh Eckroth, assistant professor of math and computer science, are closely involved in working with the students during the penetration testing, and all students in the class are required to sign non-disclosure agreements to protect information they find as part of the testing.
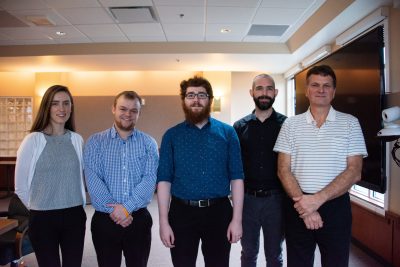
At a recent presentation on Dec. 11, 2019, to the university’s president, cabinet, deans and senior IT staff, Plante’s class discussed their results. Students Charles Mercenit, Freddie Wittmann and Madison Gipson acted as presenters for their classmates.
The work the students presented was thorough, persistent and time intensive. Since it represents attempts to penetrate the university’s network security, neither the university nor the students will be providing any concrete details, suffice to say it came down to this. Passwords.
After students spent weeks working through a series of different access points that didn’t prove fruitful, the class was able to reach a point where it appeared they just might be successful.
“When we find something, we just start digging in,” said Eckroth, and they did it by doing what real hackers would do. “Using a system in a way it wasn’t originally designed for.”
Did it work? Students in Plante’s CSEC 331 Stetson University Pentesters 2019 class ended their presentation by displaying the partial passwords of several of the administrators in attendance.

Computer science student Madison Gipson said there are three takeaways for anyone from this year’s testing:
- Random passwords are better since it takes much longer, in fact trillions of years, for password-guessing programs to crack them despite being able to run billions of password guesses per second.
- Don’t use the same password for multiple accounts. Your other accounts remain secure even if one account is hacked.
- Use Multi-Factor Authentication (MFA) if it’s offered and available. Even if your password is hacked, without access to your phone or other device, the hacker still can’t access your information.
Multi-Factor Authentication, or MFA as it’s known, will be coming to Stetson in January. MFA is the process of sending specific access codes to smartphones or other devices registered to a specific person. If you’ve ever logged onto a Google account from a new or different phone or computer, then you’ve used Multi-Factor Authentication.
On Monday, Jan. 20, 2020, staff will officially be transitioning to MFA with faculty scheduled for Feb. 3 and students on Mar. 9. Stetson Today is working with Vikram Ahmed, director of enterprise information systems, to illustrate how MFA will work for members of the community and how to sign up for and use the system.
-Bruce Chong



